Dec 27, 2018 | Kubernetes, Presentations
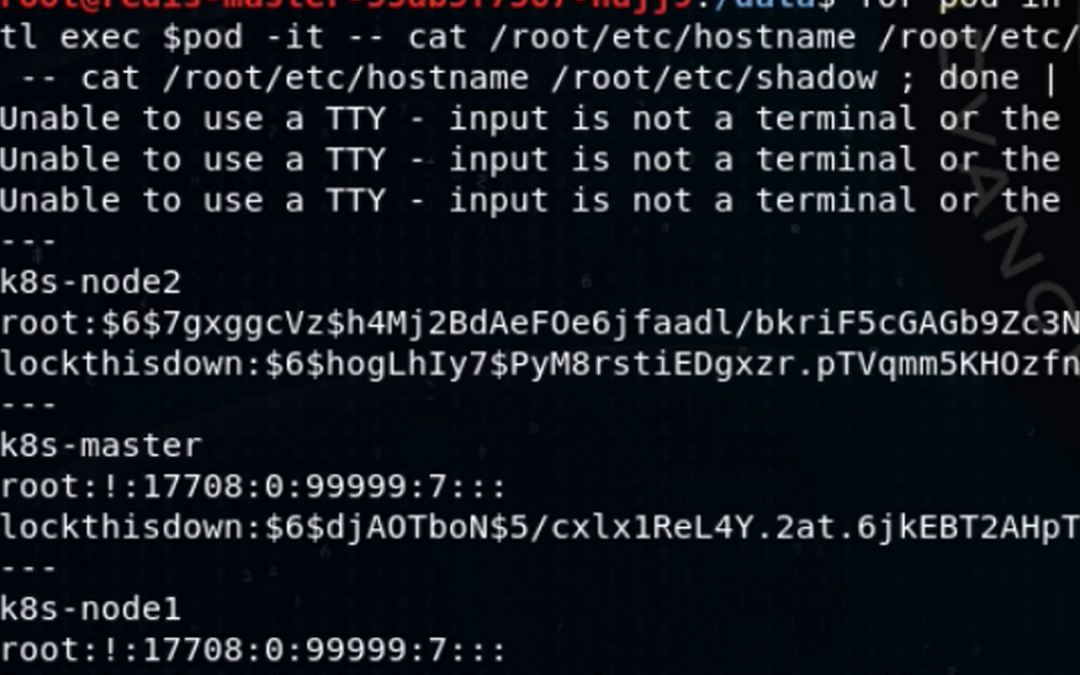
A special mini presentation by Jay Beale for this year’s KringleCon Holiday Hack Challenge. ...
Dec 12, 2018 | Blog, Kubernetes
Jay Beale created two tools used by hundreds of thousands of individuals, companies and governments, Bastille Linux and the Center for Internet Security’s first Linux/UNIX scoring tool. He has led training classes on Linux security at the Black Hat, CanSecWest,...
Nov 19, 2018 | Kubernetes, Presentations
Bust-a-Kube CTF: Attacking a Multitenant Kubernetes Cluster ...
Nov 8, 2018 | Kubernetes, Presentations, Webinars
Jay Beale returns to Kubernetes hacking, with another in his “Bust A Kube” attack and defense series. In this demo-focused on-demand webinar, Jay will attack a vulnerable Internet-based application, only to discover that the application runs in a Docker container, as...
Oct 18, 2018 | Presentations, Webinars
In this demo-heavy on-demand webinar, Jay Beale continues his history of demonstrating cyber defenses by showing how to attack and defend a real Linux system. Jay will first don his black hat, showing you how to compromise the Rick and Morty-themed “Rickdiculously...