Linux Attack and Defense: Exploiting a PHP Application and Breaking the Exploit ( Part of the BeyondTrust webinar series)
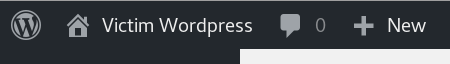
In his previous webinar, Jay Beale, co-founder and CTO of InGuardians, attacked a Linux network and demonstrated how to detect and automatically break that attack. Continuing the theme, in this webinar, Jay will put his black hat on again to attack a vulnerable...Attack and Defense Training: Saving Mr Robot’s WordPress with the Free AppArmor (Part of the BrightTalk webinar series)
In this webinar Jay Beale, co-founder and CTO of InGuardians, will demonstrate how an attacker gains access on a server running WordPress and then teach you how to break the same attack with a free, open source tool called AppArmor that’s been part of the Linux kernel...How to Attack a Linux System + Ways to Detect and Respond Swiftly ( Part of the BeyondTrust webinar series)
Bad actors continue to target our Linux systems. With a small amount of effort, we can detect their first access to the system and stop them before they move laterally. But how did they get into our systems in the first place? And what are the procedures for a swift...